Pitch Black
Inline control for networks that need a clear boundary. Pitch Black keeps the deployment model compact, the policy surface focused, and the operator workflow easy to trust.
Primary deployment is transparent inline bridge mode (L2). You can place Pitch Black pre-firewall, post-firewall, or with no firewall - it does not require a firewall to be useful.

Perimeter defense without the sprawl
Pitch Black is built for teams that want clear enforcement, clear logs, and a deployment model that stays easy to reason about.
Transparent inline (bridge-mode first)
Designed for L2 inline bridge deployments so you can add enforcement without re-architecting the network in most environments.
Policy with intent
Define what is allowed, what is denied, and what requires review without adding extra moving parts.
Logs built for investigations
Operator-readable logs for response, tuning, and internal review.
Flexible placement
Deploy pre-firewall, post-firewall, or in a firewall-less edge when that is the reality.
Remote operations
Coordinate changes and policy centrally across sites and teams.
Human-reviewed engineering
Built with disciplined iteration and engineering review to keep every claim clear, credible, and grounded in real deployment needs.
Deployment scenarios
Pitch Black is designed to sit at the outside perimeter of your network. Deploy it pre-firewall, post-firewall, or without a firewall — without turning your environment into a science project.
Pre-firewall (upstream)
Use this when you want a dedicated inline layer before traffic ever reaches your firewall. It can reduce downstream load and improve signal quality.
Form factors
One unit, shown in two form factors: inline 1U and S-unit compact.
Explore the enclosure geometry, port-facing proportions, and front-panel presence without shifting the page’s visual language.
Built for racks, built for teams
Pitch Black uses one public unit with inline 1U and S-unit compact framing. The public page keeps the hardware outline crisp so teams can review the fit before asking for the full datasheet.
- Single public unit
- 6-port mix shown above
- Built for inline bridge-mode deployments
Inline 1U
Inline perimeter deployments.

- •Single public unit
- •2x SFP+, 2x 2.5G, 2x 10G
- •Optimized for transparent bridge-mode placement
S-unit Compact
Desktop or compact edge deployments.

- •Single public unit
- •Same 6-port mix, optimized for compact framing
- •Request full specs for the complete datasheet
Operator interface snapshot
A preview of the Pitch Black operator experience — designed for clarity and operational flow. UI shown for reference; production UX may evolve.
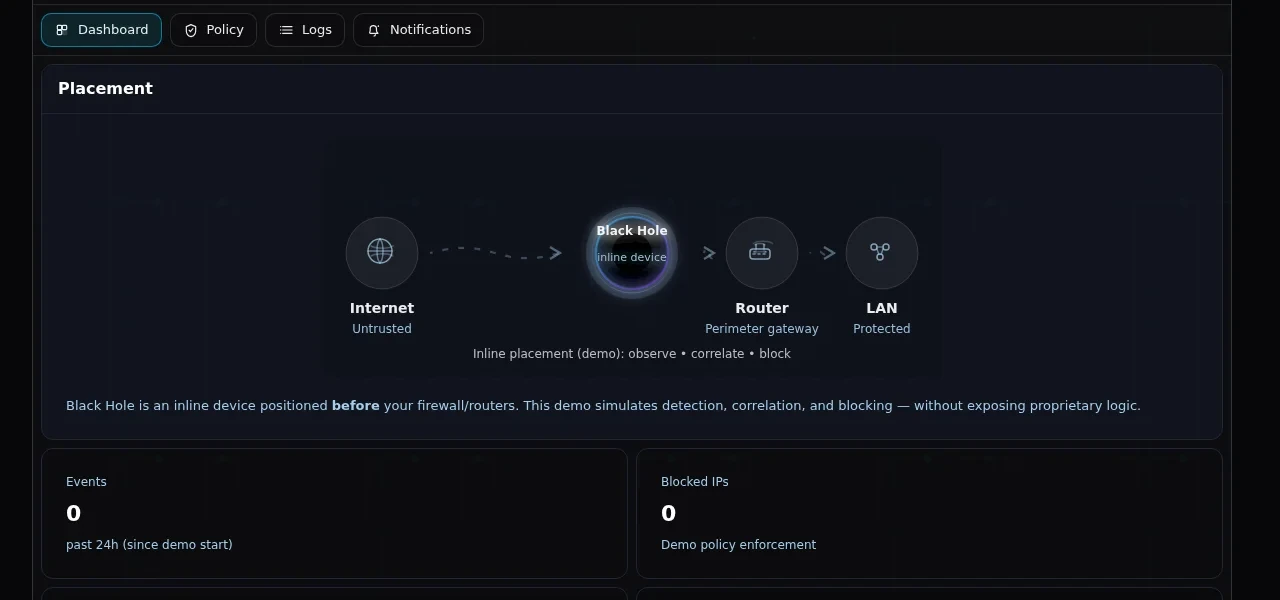
Main dashboard
A calm overview of perimeter posture, active controls, and the signals that matter.
- Status at a glance
- Operational clarity
- Designed for low-noise decisions
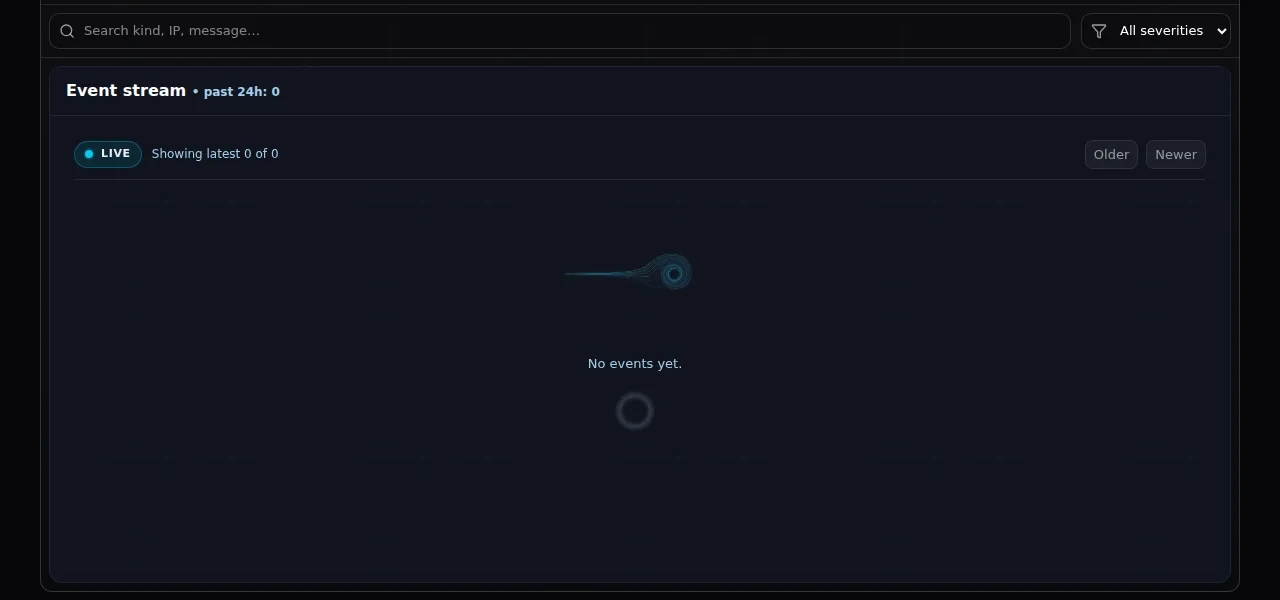
Live wire view
A real-time view of what’s traversing the perimeter, and what is being contained.
- On-the-wire telemetry
- Inline decision point visibility
- Fast investigation pivots
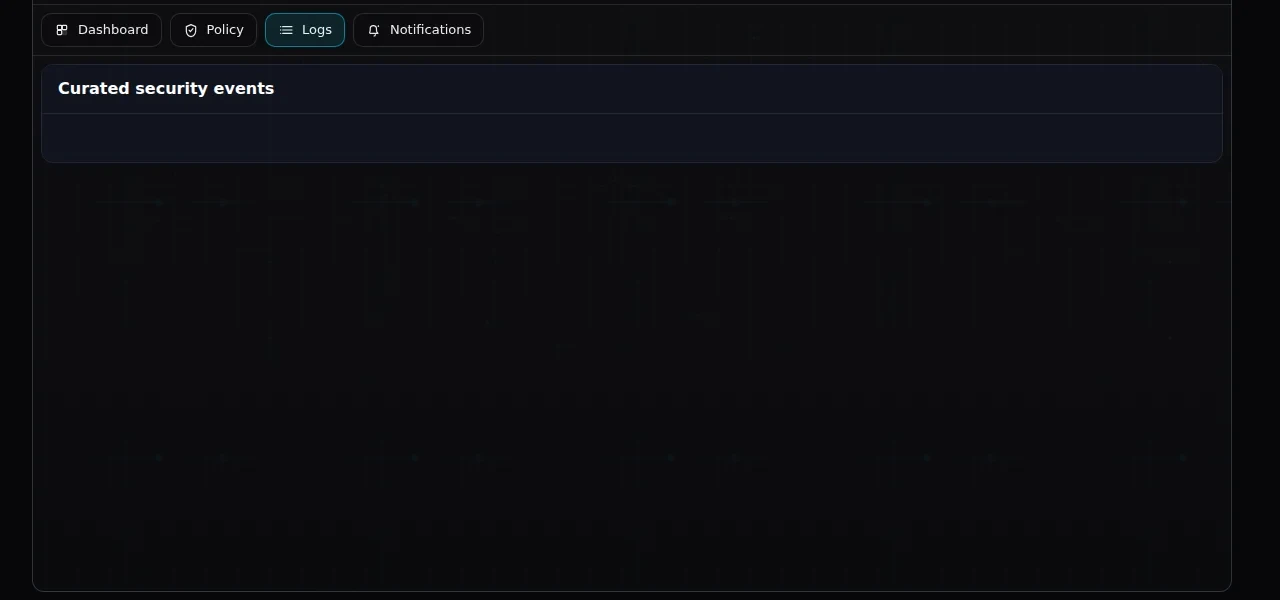
Logs
High-signal event trails meant to support investigations and post-incident review.
- Search + filter
- Audit-friendly trails
- Context that maps to operator questions
Attacker toolkit (future module)
A planned internal module for controlled scenario testing, vulnerability scanning, and network analysis-designed to pair technical metrics with IRP/DRP guidance. This is intentionally a roadmap item (not yet available) and not required for Pitch Black’s core perimeter function.
- Internal vulnerability scanning + common network metrics
- Concept: scenario-based testing for validating controls in authorized environments (not yet available)
- Report generation from observed threats and analyzed data
- IRP/DRP development guidance informed by findings
- Education-ready outputs for security awareness and training workflows
Note: roadmap items may change based on operator feedback and pilot learnings.
Pitch Black’s Quantum component integrates with ElephantSqlDB’s Quantum Cloud Database for centralized security log storage and querying-supporting investigations, reporting, and operational review.
Pitch Black remains focused on the perimeter: enforcement, policy, logging, and remote management.
Specifications (high-level)
We publish only high-confidence, operator-relevant specs here. Request full specs for the exact interface mix, performance envelope, and environmental details.
| Spec | Pitch Black |
|---|---|
| Form factor | Inline 1U / S-unit compact |
| Product family | Pitch Black |
| Network interfaces | 2x SFP+, 2x 2.5G, 2x 10G |
| Memory | Up to 48 GB DDR5 SO-DIMM |
| Storage | M.2 NVMe SSD(500 GB to 1 TB configurations) |
| Power | 12V/5A DC input |
| Material | Aluminium alloy |
| Operating temperature | 0–50°C |
| Primary mode | Transparent inline bridge mode (L2) |
| Placement options | Pre-firewall, post-firewall, or no firewall |
| Management | Remote management + centralized policy |
| Logging | Operator-grade logging |
Capabilities
Focused features — built to be used, not to sprawl.
Inline enforcement
A dedicated inline decision point at the perimeter — designed to keep enforcement clear and controllable.
Central policy
One policy source for consistent behavior across sites and deployments.
Operator-grade logging
High-signal event trails that support response, review, and accountability.
Remote management
Manage deployments and changes across sites with a controlled workflow.
Flexible placement
Pre-firewall, post-firewall, or no firewall — choose what fits your perimeter reality.
Hardware-enforced perimeter layer
A physical appliance engineered for consistent behavior at the edge.
Modern Ethernet fit
Designed around practical 2.5GbE and 10GbE environments (full specs available on request).
Verification-first posture
We keep public claims grounded in what can be procured, deployed, and explained clearly.
Use cases
Branch & retail edges
Standardize enforcement and logging across many small sites.
Datacenter ingress/egress
Add a focused inline layer adjacent to your existing perimeter controls.
Firewall-adjacent hardening
Deploy alongside an existing firewall to reduce downstream pressure and increase signal quality.
Firewall-less environments
For networks without a firewall, Pitch Black can still serve as an inline perimeter enforcement and logging layer.
Why you should be confident
Pitch Black is built for teams that have to justify every perimeter decision to operations, security leadership, and procurement. Clear scope, predictable behavior, and review-ready visibility are part of the product experience.
Validated before it ships
Every capability is validated against real deployment scenarios before it ships — so what you evaluate is what you operate.
Predictable change behavior
Controlled updates and operational visibility help teams manage change intentionally across sites and environments.
Operator-readable by design
Logs, policy language, and management workflows are built for engineers who need fast answers during production incidents and routine review.
Procurement-safe specifications
The public page covers what technical evaluators and buyers need to assess fit. Full datasheets and deployment guidance are available through the normal procurement process.
Deployment that fits your topology
Pre-firewall, post-firewall, or no firewall — Pitch Black is designed to fit the network you have without forcing unnecessary redesign.
Claims grounded in what ships
Public capabilities are described in operational terms that can be reviewed, validated, and supported in real deployments.
FAQ
High-signal answers to the questions enterprise teams ask first.
Request a Pitch Black demo
Send your topology and port needs. We’ll respond with the right form factor guidance and the launch brief.
Public details stay procurement-safe. Request the full datasheet if certification language or deeper interface detail matters for your review.


